


Common packet filters like MacOS’s PF do not allow packets to pass through the firewall unless they match a user defined and established set of rules. PF can filter traffic based on many packet attributes like source and destination IP addresses and ports, protocol, and many others.
Packet filter rules affect all apps running on the system. Network firewall are unable to pass/block specific applications as they are not aware of which application is making a connection.
PF is the MacOS built in network firewall and can be configured using the shell terminal or third party apps like Murus. Murus is a graphic user interface front end for PF. Use Murus to configure a packet filter rule set. The main purpose is protecting services running on your Mac from remote inspection or intrusion. It can also be used to forcibly constrain its access to the network by limiting the available outbound services. Being a network firewall front end, Murus offers many more options and features including proactivity, port-knocking, bandwidth management, NAT gateway, logs analysis, notifications, and much more.
Application firewalls, unlike network firewalls, are able to identify which app is trying to initiate or receive a connection.
On inspecting all packets for improper content, application firewalls can restrict or prevent outright the spread of viruses, worms and trojans or simply block the leak of data by chatty apps.
Socket filters function by determining whether a process should make any given connection. Application firewalls accomplish their function by hooking into socket calls to filter the connections between the application layer and the lower layers of the OSI model.
ALF is the MacOS built-in application firewall and can be configured from MacOS System Preferences to filter only inbound connections.
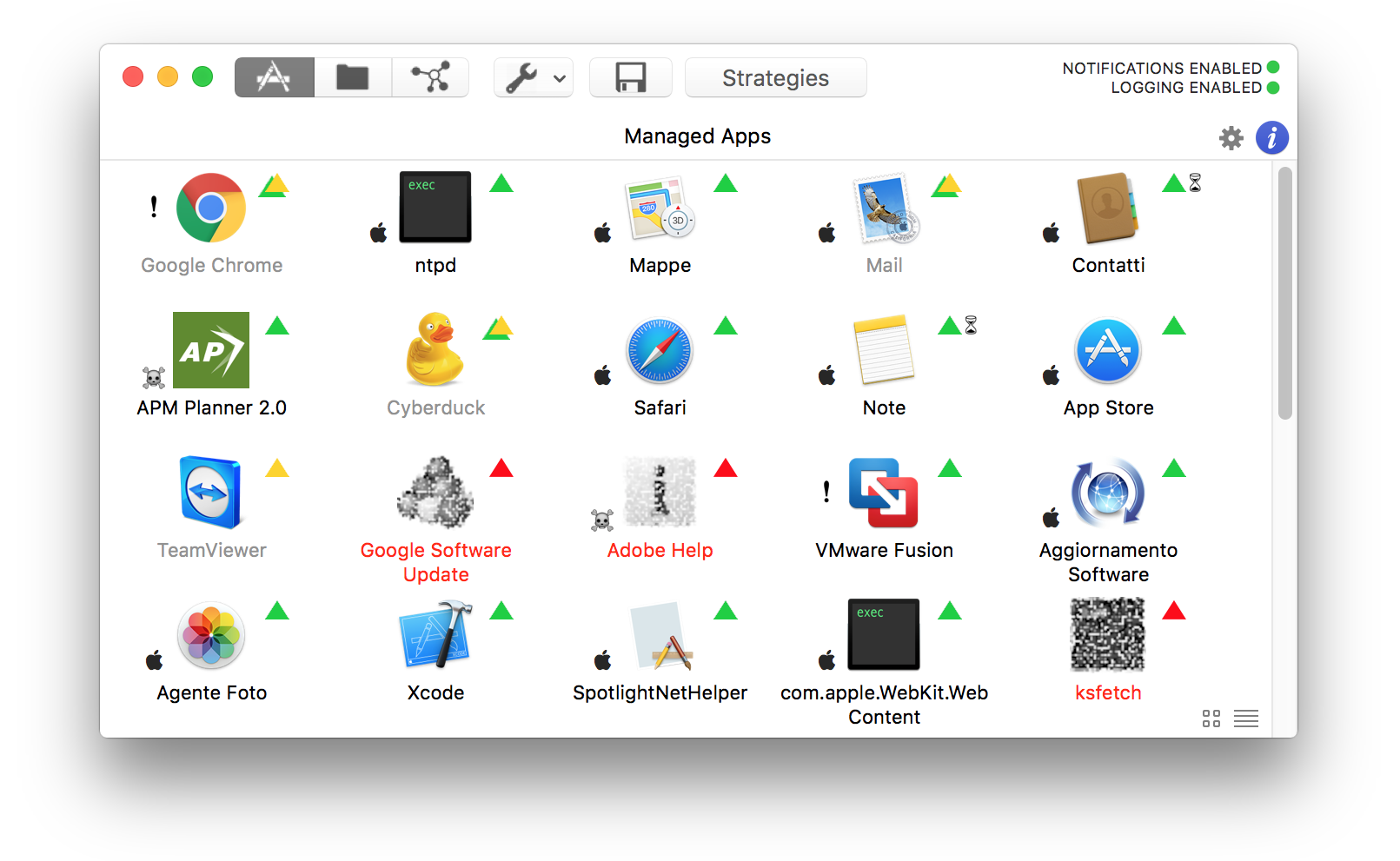
Vallum is an application firewall and is a much more powerful and flexible alternative to ALF. It’s main purpose is to monitor and block apps connections. Each app running on your Mac can have its specific set of rules, matching packets for IP addresses, subnets, ports and port ranges, and each app can be set to apply these rules silently and automatically or asking the user with popup notification alerts.
System wide rules affect all apps and services
Build and control a network infrastructure
Low latency, highly efficient packet filtering
Each app has its own rules
Intercept unwanted traffic by legit apps or malware
Interact with the firewall in real time with notifications alerts